It took me quite a while but eventually I got it working: Using Pidgin on Linux Mint and connect it to the company's Lync 2013 server. I installed the following packages:
sudo apt-get install pidgin pidgin-sipe
Afterwards I needed to handle quite a few hickups.
Problem 1: Self-Signed certificates
The first problem was that the internal SIP server had self-signed certificates and Pidgin refused to connect to the server:
(10:24:14) proxy: Connected to sipserver01:5061.
(10:24:14) nss: subject=CN=sipserver01.company.local,OU=IT,O=Company,L=Zuerich,ST=Zuerich,C=CH issuer=CN=Company CA,O=Company,C=CH
(10:24:14) nss: partial certificate chain
(10:24:14) certificate/x509/tls_cached: Starting verify for sipserver01
(10:24:14) certificate/x509/tls_cached: Checking for cached cert...
(10:24:14) certificate/x509/tls_cached: ...Not in cache
(10:24:14) nss: CERT 0. CN=sipserver01.nzzmg.local,OU=IT,O=Company,L=Zuerich,ST=Zuerich,C=CH :
(10:24:14) nss: ERROR -8179: SEC_ERROR_UNKNOWN_ISSUER
(10:24:14) certificate: Failed to verify certificate for poolzh01
(10:24:14) connection: Connection error on 0x7fc15343b8f0 (reason: 0 description: SSL peer presented an invalid certificate)
Although there are a lot of pidgin bugs/requests open to allow self-signed certificates, there is a manual workaround. I downloaded the SSL certificate by using the following openssl command:
openssl s_client -connect sip.company.local:443
This gave me the output of the server's first certificate and the information with which certificate it was signed. This turned out to be another self-signed CA certificate which was deployed on all Windows workstations.
In order to get the CA certificate I went into a Windows machine running in the company's domain, I did the following steps:
Open Internet Explorer -> Internet Options -> Content (Inhalte in German) -> Certificates -> Intermediate Certification Authorities (Zwischenzertifizierungsstellen)
In my case, the company's CA certificate could be selected in this list and I exported it as Base-64 coded X509 certificate.
Now that I got both certificates (the main server certificate plus it's issuing certificate), I saved them in the following paths:
However this was still not sufficiant because Pidgin reported that the Company CA certificate was not trusted. So I needed to copy the CA certificate into /etc/ssl/certs, too. After this, first success:
(10:39:13) certificate/x509/ca: Lazy init completed.
(10:39:13) nss/x509: Exporting certificate to /home/admck/.purple/certificates/x509/tls_peers/sipserver.company.local
(10:39:13) util: Writing file /home/admck/.purple/certificates/x509/tls_peers/sipserver.company.local
(10:39:13) nss: Trusting CN=sipserver01.company.local,OU=IT,O=Company,L=Zuerich,ST=Zuerich,C=CH
(10:39:13) certificate: Successfully verified certificate for sipserver.company.local
(10:39:13) stun: using server
Problem 2: Authentication problems - update pidgin-sipe plugin
I found a lot of pages describing different Pidgin settings to connect to Lync, here are some:
I tried all kinds of combination using NTLM, Auto, TLS authentication, etc. I got a "401 - Unauthorized: Access is denied due to invalid credentials", later a "certificate request failed", depending on the settings.
Eventually I decided to try the newest piding-sipe plugin (as of this writing 1.20). Unfortunately in Linux Mint 13.7 (and therefore Ubuntu 14.04 trusty), the package version is at 1.17. I decided to add a PPA repository which contained the new version:
sudo add-apt-repository ppa:sipe-collab/ppa
You are about to add the following PPA to your system:
More info: https://launchpad.net/~sipe-collab/+archive/ubuntu/ppa
Press [ENTER] to continue or ctrl-c to cancel adding it
Executing: gpg --ignore-time-conflict --no-options --no-default-keyring --homedir /tmp/tmp.LiRa3uJQ8z --no-auto-check-trustdb --trust-model always --keyring /etc/apt/trusted.gpg --primary-keyring /etc/apt/trusted.gpg --keyserver hkp://keyserver.ubuntu.com:80 --recv-keys F93FF666
gpg: requesting key F93FF666 from hkp server keyserver.ubuntu.com
gpg: key F93FF666: public key "Launchpad PPA for Sipe plugin collaboration" imported
gpg: Total number processed: 1
gpg: imported: 1 (RSA: 1)
And then installed the new version:
sudo apt-get install pidgin-sipe
[...]
The following packages will be upgraded:
libnice10 libpurple0 pidgin pidgin-data pidgin-sipe
[...]
Besides showing more details in the debug log, the new pidgin-sipe version also offered an additional authentication mechanism (but it's not needed in this case).
Solving it: Using the correct settings
Although I updated pidgin-sipe to the newest version, the same errors still appeared: "sipe certificate request CertProvisioningService.svc failed" and other failures with "Webticket failed". Finally I got it working with the follwing account settings:
[ Basic ]
Protocol: Office Communicator
Username: myemail@company.local
Login: Empty
Password: mypassword
Local alias: Empty
[ Advanced ]
Server[:Port]: Empty
Connection type: Auto
User Agent: UCCAPI/4.0.7577.0 OC/4.0.7577.0 (Microsoft Lync 2010)
Authentication scheme: Auto
Use Single Sign-On: Not checked
The fact that server/port is left empty requires a correct DNS setup for your domaine. Check out https://technet.microsoft.com/en-us/library/gg398758%28v=ocs.15%29.aspx for more information.
Interestingly, the User Agent seems to be very important for the connection.
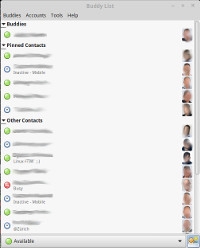
With these settings I was finally able to connect to the Lync server with Pidgin!
Claudio Kuenzler from Switzerland wrote on Jul 13th, 2016:
Unfortunately only IM. But I'm not sure whether this is a Pidgin or a Lync connection problem.
Patrick Rynhart from New Zealand wrote on Jul 13th, 2016:
Awesome! Are you able to do Voice Calls ? Or IM only ? Thanks, Patrick

AWS Android Ansible Apache Apple Atlassian BSD Backup Bash Bluecoat CMS Chef Cloud Coding Consul Containers CouchDB DB DNS Database Databases Docker ELK Elasticsearch Filebeat FreeBSD Galera Git GlusterFS Grafana Graphics HAProxy HTML Hacks Hardware Icinga Influx Internet Java KVM Kibana Kodi Kubernetes LVM LXC Linux Logstash Mac Macintosh Mail MariaDB Minio MongoDB Monitoring Multimedia MySQL NFS Nagios Network Nginx OSSEC OTRS Observability Office OpenSearch PGSQL PHP Perl Personal PostgreSQL Postgres PowerDNS Proxmox Proxy Python Rancher Rant Redis Roundcube SSL Samba Seafile Security Shell SmartOS Solaris Surveillance Systemd TLS Tomcat Ubuntu Unix VMWare VMware Varnish Virtualization Windows Wireless Wordpress Wyse ZFS Zoneminder